Table of Contents
Home > FAQ > Email > General > What is Email Spoofing?
What is Email Spoofing?
Email spoofing is when someone sends an email pretending to be someone they are not. Such email appears to be originated from a trusted sender - such as customers, vendors, coworkers or managers, or even yourself - but they are actually sent from cyber-criminals, who would trick you into transferring money to them, downloading an attachment with malware that could infect to your entire network, providing them your personal information for fraudulent purposes, and more.
Here are some of the examples of spoof mail:
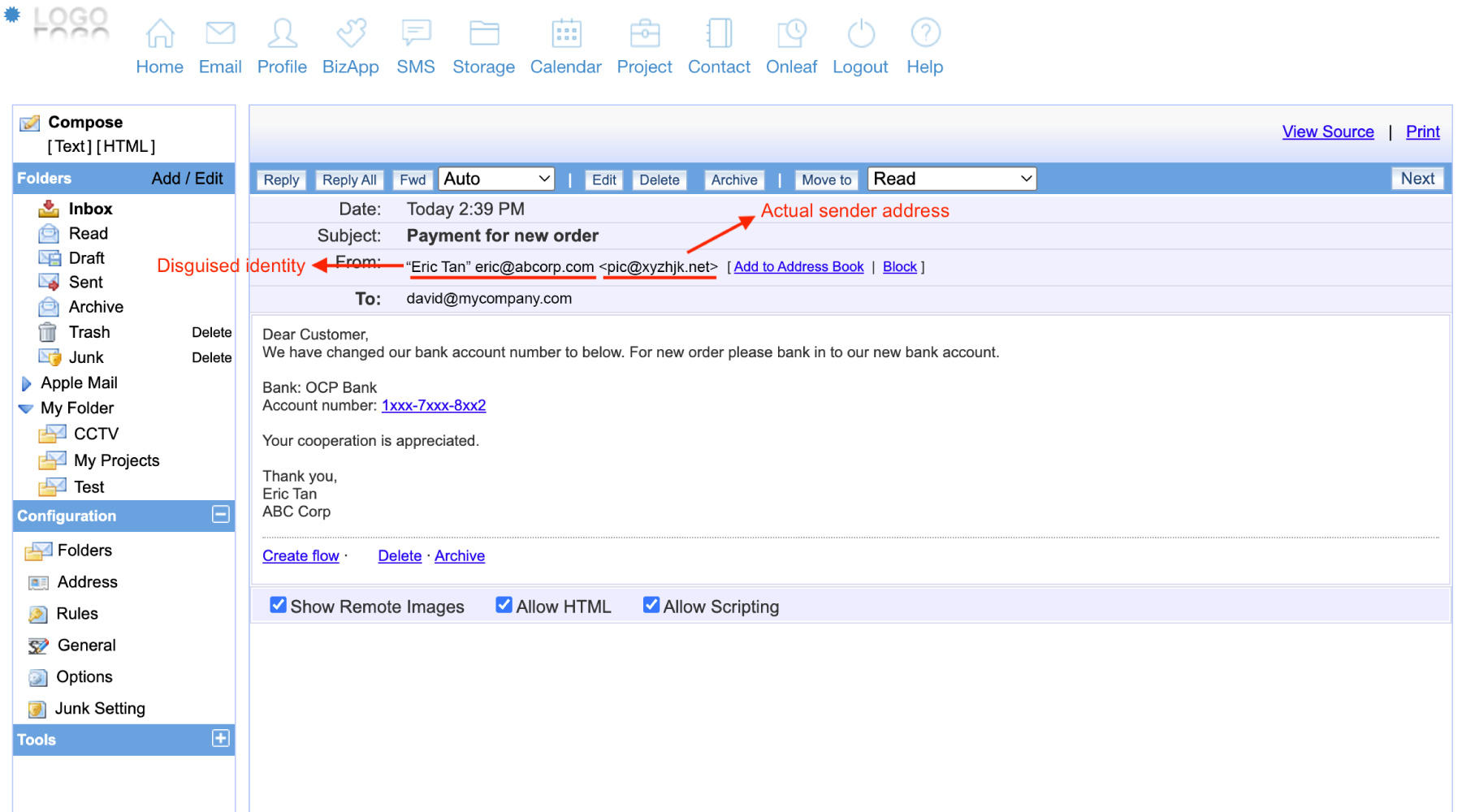
Example 1
In the example below, the sender is pretending to be your regular contact, trying to trick you to make payment to another bank account. If we look closely on the email, we will notice that the sender email address is “pic@xyzhjk.net” instead of Eric from eric@abcorp.com. Although the mail content looks legitimate, with professional-looking email signature, we should always be careful and double check on the sender email address before we make any response to the sender.
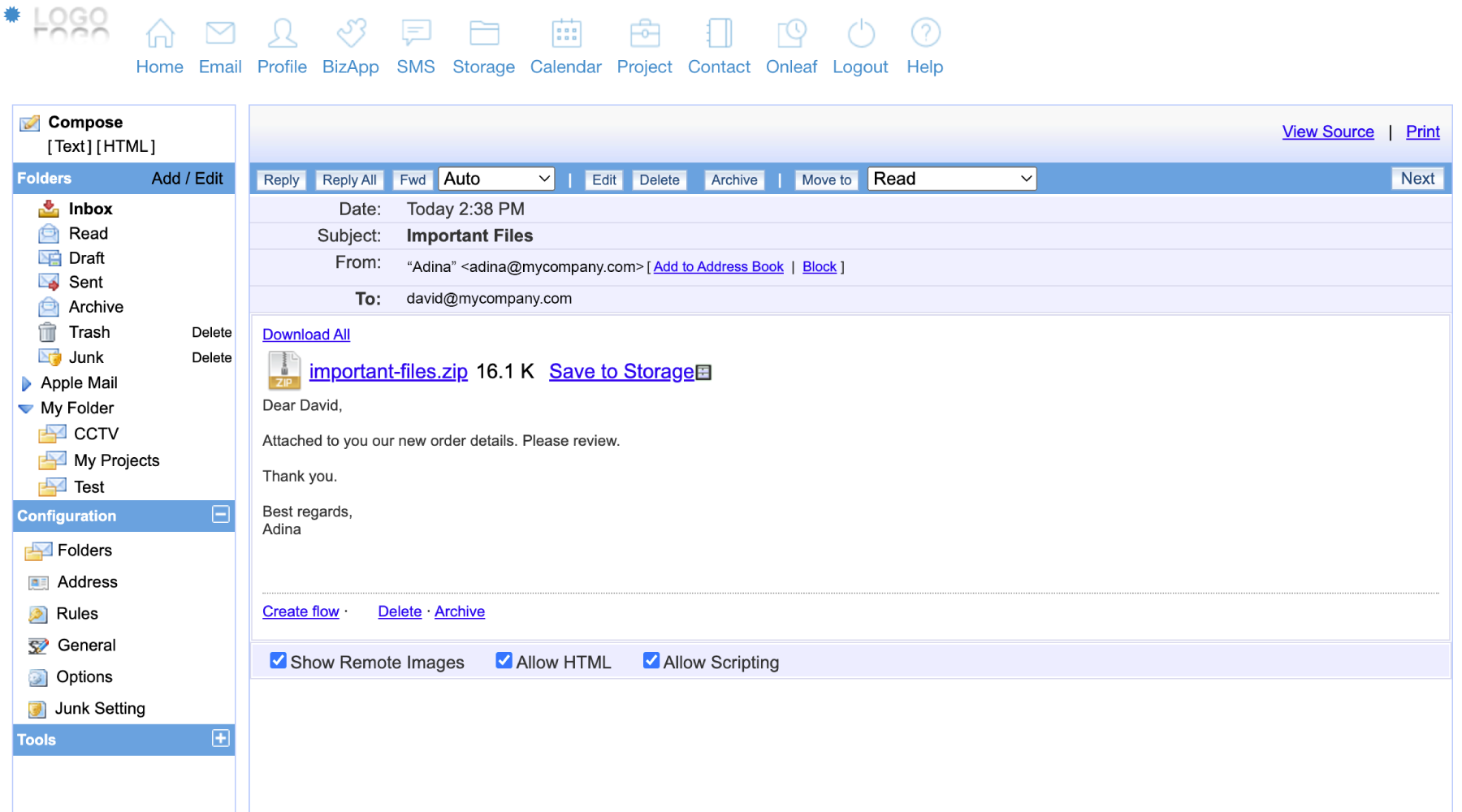
Example 2
In this example, the sender is sending an email using your actual domain or an actual email address from your domain, though it was sent from a different server/IP. Such spoof mails are usually blocked by the server by default. However, if your SPF record includes the third-party server/IP, these emails may still be delivered. We recommend reviewing your SPF record and only allowing legitimate third-party servers to send emails on behalf of your domain.
Identifying Spam
To protect the safety of our email account, we need to stay vigilant and equip ourselves with the knowledge of identifying scam and spam mails. When we receive emails from vendors or suppliers who inform about change of payment details, or emails from regular contacts that contain suspicious attachments, always verify with the senders first before responding or taking any actions.
For more information on how to identify a spam mail, please refer to this article: How to identify whether an email is a spam mail?